Table of contents
- Part 1
Integrate Basic Security Into Your Java Web Apps
- 1
Get the Most Out of This Course
- 2
Identify the Value of Security Within Web Applications
- 3
Use Spring Security in Your Spring Boot App
- 4
Identify How to Secure Access to an App Using Authentication and Authorization
- 5
Configure Role-Based Access Control
Quiz: Integrate Basic Security Into Your Java Web Apps
- Part 2
Create a Secure Login for Your Spring App With OAuth 2.0
- Part 3
Leverage Security Techniques Provided Within Spring Security
Table of contents
- Part 1
Integrate Basic Security Into Your Java Web Apps
- 1
Get the Most Out of This Course
- 2
Identify the Value of Security Within Web Applications
- 3
Use Spring Security in Your Spring Boot App
- 4
Identify How to Secure Access to an App Using Authentication and Authorization
- 5
Configure Role-Based Access Control
Quiz: Integrate Basic Security Into Your Java Web Apps
- Part 2
Create a Secure Login for Your Spring App With OAuth 2.0
- Part 3
Leverage Security Techniques Provided Within Spring Security
Identify the Value of Security Within Web Applications
By now, you’re well on your way to being a Java developer on the extensive Java platform. It’s been a lot of hard work, and you’re excited to finally develop some quality apps - and that means making them secure.
So now, I have some news for you: web applications have increasingly been the target of malicious attacks.
How does this happen?
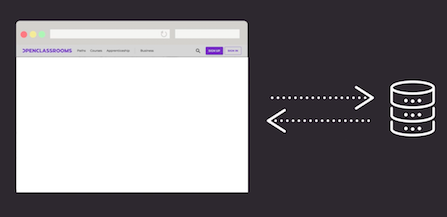
A computer's browser accesses a web application and connects the user to a database. This database can be used to retrieve or store data processed on the web browser.
As more companies have started to conduct business on the web, more proprietary data and personally identifiable information are passed on the networks from server to server around the world. Although this data should be protected, many web developers and businesses do not have the know-how to secure this data when it is stored or in transmission. In other words, due to the sophisticated attacks that are common these days, web applications are vulnerable unless specific measures are taken to prevent them.
Most of the attacks we hear about effect some of the larger businesses such as Yahoo, Facebook, and Marriott. Still, there are even more that occur daily on web applications that belong to smaller companies. Typically, a lot of these businesses are targeted for trade secrets or client information. Malicious users make a lot of these attacks, and the stolen data can be used for personal or financial gain.
Let’s look at some key examples starting with a typical attack: data breaches. In September of 2018, Marriott experienced one of the most significant data breaches in history. It affected 500 million customers and cost the company $3 million. Customer PII (personally identifiable information) was compromised when they used the reservation system meaning that Marriott lost control over a customer’s name, address, credit card info, and anything else used when making a reservation on the Marriott website. The sad part is that this breach started in 2014 and wasn't discovered until 2018. Yahoo and Equifax experienced similar data breaches.
Another typical attack made on web applications is injection. Research has put them in the number one spot for most common web application attacks with the SQL injection as the most popular. 😣
An SQL injection happens a lot in web sites where users have to fill out information like a login page. The hacker can put SQL code in the username field that can break the entire web application. In June of 2019, Akamai, a cloud-based provider that gets security alerts for SQL injection attacks, reported that the incidents of SQL attacks are on the rise in the gaming industry.
The methods used to prevent SQL injections require some know-how from the front-end and backend developer. If both parties can work in unison to safeguard the web application from an SQL injection, they have done their part in protecting it from an attack by malicious users. Whether you’re a front-end, backend, or full-stack web developer, you play a significant role in securing your web application.
Securing Your Applications
Now you know why you need to pay attention to security. And as a Java developer, you help prevent your company from experiencing such a breach.
How do I ensure my applications are secure?

First, you want to look at some of the available research. A non-profit organization called Open Web Application Security Project (OWASP) was created to study and educate the public on the most common attacks made on web applications and what can be done to prevent them. If you can set up your Java application with attention to the OWASP top ten standards, you will have created a high-quality app and can consider yourself a great developer.
Next, you want to choose solid building blocks. A vulnerable framework is a recipe for disaster, so find out if a framework or dependencies (plugins, libraries, and other frameworks) have a reputation for being reliable. Additionally, you also want to take the extra step of securing your web applications from frequent attacks and testing them - which we will talk about later in this course. 😄
That seems a little overwhelming. Where do I even start?
As a developer, you can do your due diligence to block many of the frequent attacks by using code libraries aimed at securing your web applications. For Java developers, these libraries exist for all kinds of web application frameworks, including Spring Boot, Maven, and Java applications.
Spring Security is a framework that provides an easy to use solution for Java applications - especially with Spring Boot. It autoconfigures secure programming components that can help you prevent attacks with little to no configuration. We'll explore how Spring Security works and how to use it throughout this course.
Let’s Recap!
Malicious attacks targeting web applications are on the rise.
Two common attacks are data breaches and SQL injection.
You have to start secure programming to prevent common attacks.
OWASP defines a collection of the top ten attacks targeting web applications.
In the next chapter, we'll look at how you can use Spring Security to battle these issues and more!
Ever considered an OpenClassrooms diploma?
- Up to 100% of your training program funded
- Flexible start date
- Career-focused projects
- Individual mentoring
Find the training program and funding option that suits you best
